The nOAuth “flaw” is a symptom of industry antipatterns
If you haven’t followed the news recently, Descope released an article diving into how their security researchers were able to abuse OpenID Connect (OIDC) ID token claims to spoof the user they are authenticating as for multi-tenant SaaS applications. You can read their research article here, nOAuth: How Microsoft OAuth Misconfiguration Can Lead to Full Account Takeover (descope.com).
In conjunction with this, Microsoft has updated developer guidance for OpenID Connect and SAML assertions, and provided a blog post covering all of this, which can be found here, The False Identifier Anti-pattern (microsoft.com).
Multi-tenant SaaS applications are those applications, such as Canva or Sessionize, which allow you to authenticate with your Microsoft or Office 365 account. Without getting off track, this is what allows SaaS application vendors to develop applications that can integrate with an organizations Azure Active Directory environment requiring no effort on the part of administrators.
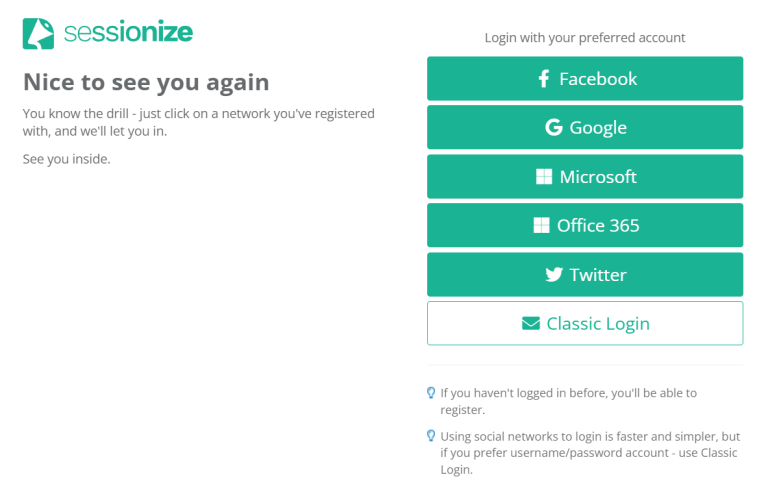
The Sessionize authentication screen allowing a user to select their identity provider.
And as it goes whenever there is a security problem, someone must fall on the sword. In this case Microsoft is taking the hit; unfortunately most new articles are incorrectly reporting on this as an Azure AD “flaw” that Microsoft had to “fix”. Kudos to Kurt Mackie (@kurmac) at Redmond Mag for being the only article to accurately report on this problem, which you can find here, Microsoft Advises App Developers About ‘nOAuth’ Attack Route — Redmondmag.com. To be fair, Microsoft isn’t completely innocent, as it took a case like this to really have them sharpen their guidance from a bit of a softer stance, but this is not really a technical flaw. I suppose we can’t blame others for not wanting to write articles about developers using antipatterns.
