Authenticator App: IOS Multiple Passwordless Account Support Is Here!¶
For anyone who lives in a world of multiple Azure AD accounts and the Authenticator App, you can finally rejoice over not having to make the difficult decision over which account is the one you enable for passwordless… or potentially not having to carry multiple devices.
To date, you could enroll one Azure AD account and one personal Microsoft Account (MSA) for passwordless in the Authenticator App. Even with multiple Azure AD accounts in the same tenant, only one could go passwordless.
With this update, not only can you go passwordless for multiple accounts in the same Azure AD tenant, but across multiple tenants as well.
Enabling the preview¶
First you’ll want to make sure you have the latest version of the MS Authenticator App from the Apple App Store, which you can check here, Microsoft Authenticator on the App Store (apple.com).
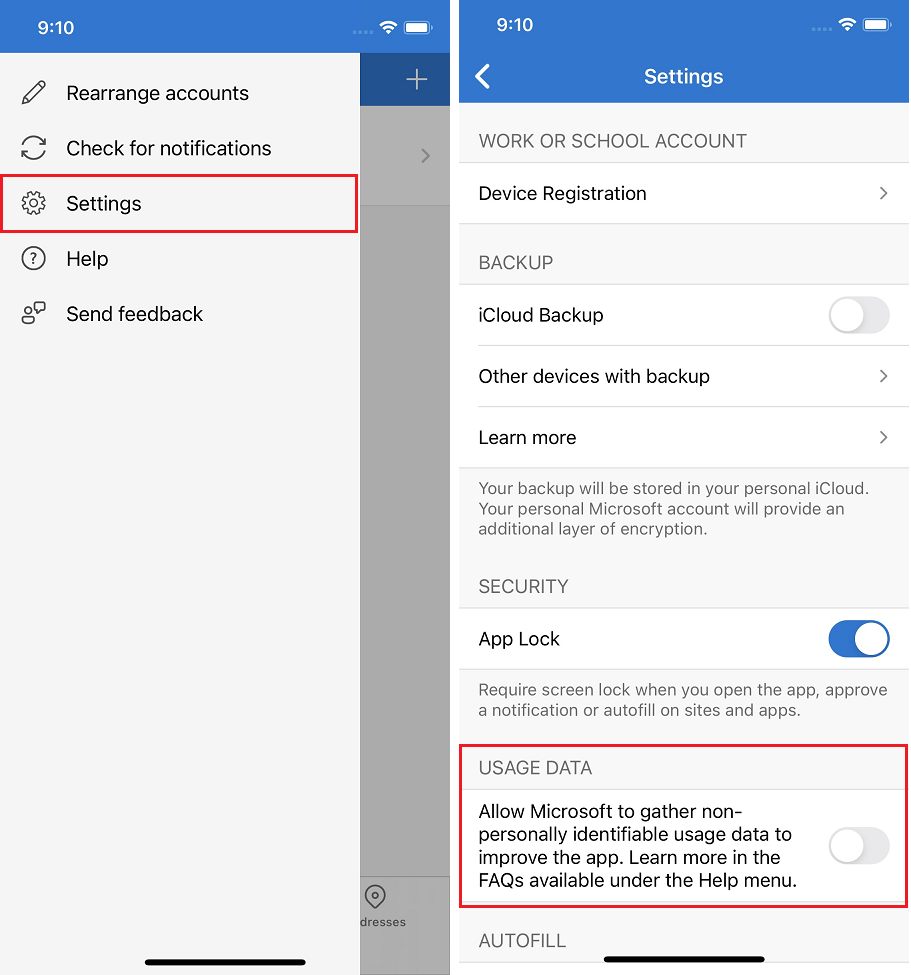
Per Microsoft, you’ll also need to enable a usage data setting within the Settings of the Authenticator App. You can do this by opening the hamburger menu in the upper left, and select Settings.
Within settings, you’ll want to enable Usage Data (the screenshot shows it disabled, but you need to enable it). The associated MS Docs article is here, Passwordless sign-in with Microsoft Authenticator – Azure Active Directory – Microsoft Entra | Microsoft Docs.
Note
In my testing I found you need to force quit the Authenticator App after enabling Usage Data to allow for multiple account enrollment.
Multiple passwordless accounts in the same Azure AD tenant¶
On each additional account you want to go passwordless, select the account in the Authenticator App, and choose Enable phone sign-in. This is the same as the experience to enable for the first account, with an exception that you do not need to register the device again.
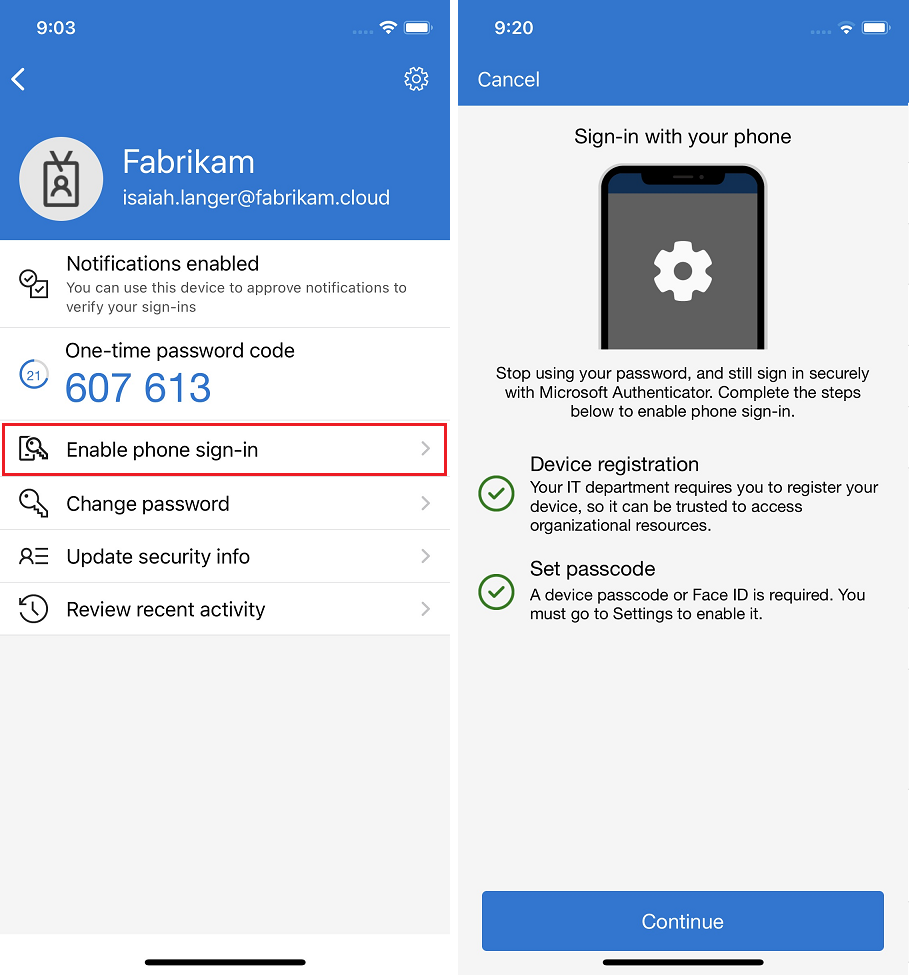
You’ll see that the device indicates it is already registered, just select Continue.
Info
You will be prompted to perform MFA if you have not recently authenticated on the device.
Multiple passwordless accounts in different Azure AD tenants¶
If your accounts exist across multiple Azure AD tenants, you can still initiate it through the same process as above, select the additional account, and select Enable phone sign-in. During this process, the device will just require you to register it within that second Azure AD tenant.
After device registration is completed, passwordless will be enabled for both accounts in both tenants.
We can examine this within the Authenticator App, by browsing to Settings, Device Registration, where we see the tenants the device is registered with.
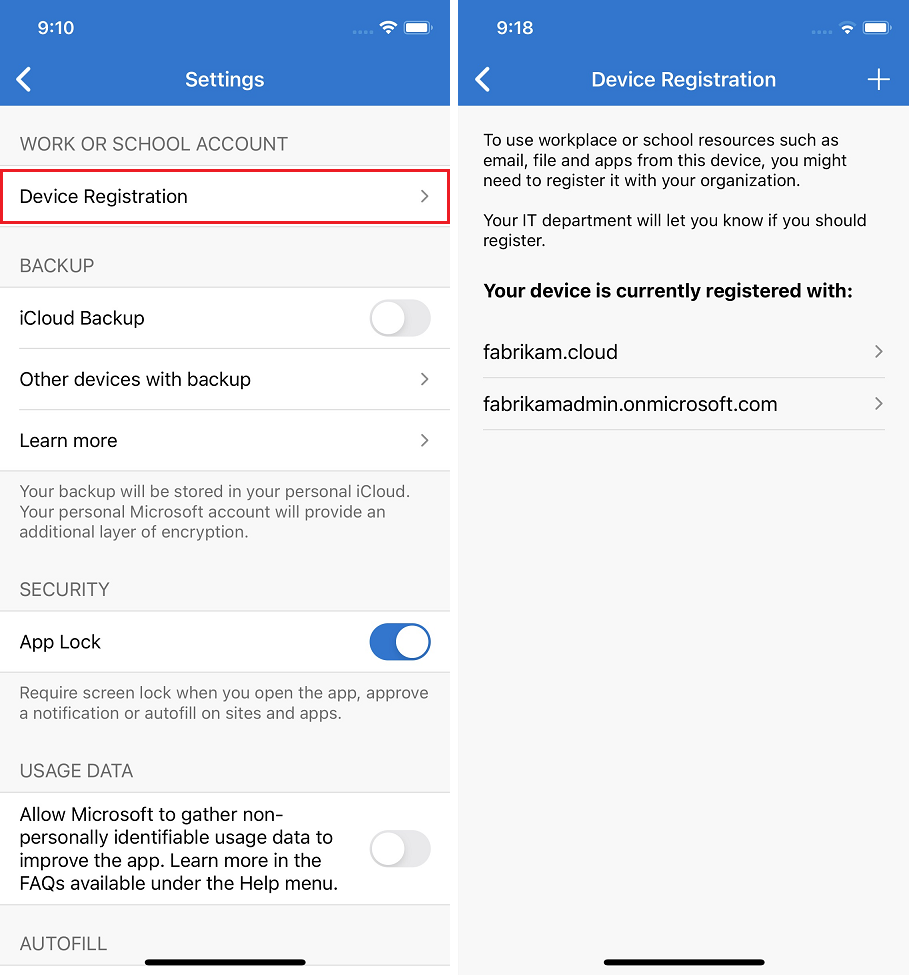
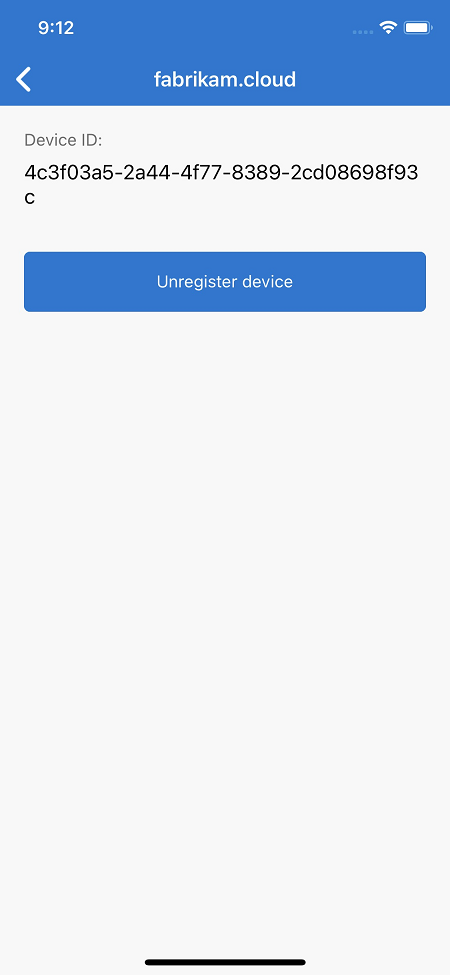
You can drill further into each tenant within the settings, see the Device ID, and optionally unregister the device from said tenant.
If the device is unregistered from an Azure AD tenant, the associated accounts will automatically be disabled for passwordless on it.
Note that the Device ID is unique per Azure AD tenant.
The experience¶
I’ve been testing this experience in a private preview for a while now, and I’ll say it’s been as smooth as one could want. Naturally, as the private preview recommends not using preview software for production use, I immediately installed it on my primary iPhone and enabled all of my Azure AD accounts for passwordless. I currently have multiple accounts enabled for passwordless across three Azure AD tenants, to which I’ve authenticated multiple times a week, and an issue has not arisen.
Final thoughts¶
This is a simple yet fantastic step forward in the passwordless journey by Microsoft; while not everyone out there has multiple Azure AD accounts, for those of us that do, we finally don’t have to make choices anymore.
For organizations out there who have not gone passwordless, because of concerns about push notification fatigue, now is the time to enable push notifications and allow for passwordless authentication for our end users. With the addition of number matching and additional context, we can protect our organizations from accidental notification approval, which I cover here, Azure AD: Increasing Security within the MFA Experience – Eric on Identity.
To provide a great user experience, we need to not lock our users into a singular means of strong authentication, and allowing users to choose the strong authentication experience that works best for them promotes better end user habits and better organizational security.